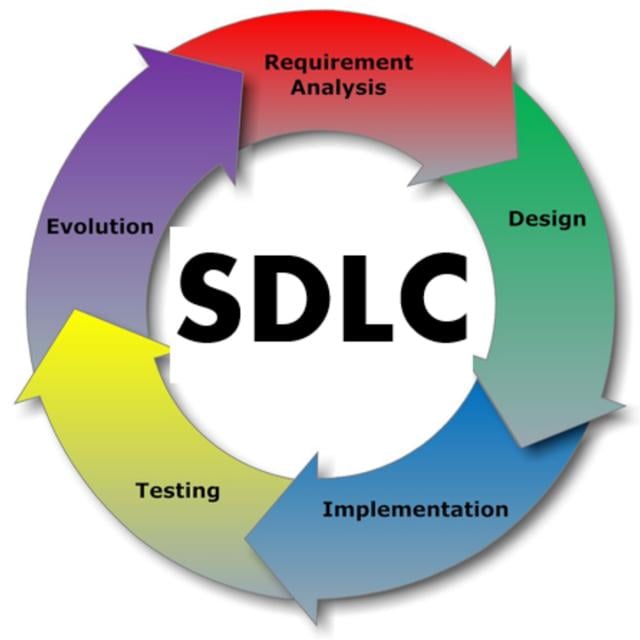
This course we will explore the foundations of software security. We will consider important software vulnerabilities and attacks that exploit them -- such as buffer overflows, SQL injection, and session hijacking -- and we will consider defenses that prevent or mitigate these attacks, including advanced testing and program analysis techniques. Importantly, we take a "build security in" mentality, considering techniques at each phase of the development cycle that can be used to strengthen the security of software systems.
Class Deals by MOOC List - Click here and see Coursera's Active Discounts, Deals, and Promo Codes.
Successful learners in this course typically have completed sophomore/junior-level undergraduate work in a technical field, have some familiarity with programming, ideally in C/C++ and one other "managed" program language (like ML or Java), and have prior exposure to algorithms. Students not familiar with these languages but with others can improve their skills through online web tutorials.
Course 2 of 5 in the Cybersecurity Specialization.
Syllabus
WEEK 1
Overview
Overview and expectations of the course
Low-level security
Low-level security: Attacks and exploits
WEEK 2
Defending against low-level exploits
Defending against low-level exploits
WEEK 3
Web security
Web security: Attacks and defenses
WEEK 4
Secure software development
Designing and Building Secure Software
WEEK 5
Program analysis
Static Program Analysis
WEEK 6
Pen testing
Penetration and Fuzz Testing